The quantum-computing revolution is upon us — a paradigm shift in computing power that harnesses the laws of quantum mechanics to solve problems far too complex for today’s classical digital computers.
Quantum computers apply the unique behavior of quantum physics to computing, introducing unprecedented capabilities to traditional programming methods. From transforming drug research, energy use, manufacturing, cybersecurity and communications to enhancing AI applications, autonomous-vehicle navigation, financial modelling and more — quantum is poised to unlock a new reality.
The emerging quantum-computing industry is already making enormous advances — as more organizations discover its potential, the global market is expected to hit US$50 billion by the end of this decade.1 Major technology companies are rapidly developing their quantum capabilities — Amazon, IBM, Google and Microsoft, for example, have already launched commercial quantum-computing cloud services, and there are significant investments in new players such as Quantinuum and PsiQuantum.
KPMG in Canada surveyed 250 large corporations and found that about 60 percent of organizations in Canada and 78 percent in the US expect quantum computers to become mainstream by 2030.2 But as quantum proliferates, so do concerns about its potential impact on cybersecurity.
Most businesses surveyed are “extremely concerned” about quantum computing’s potential to break through their data encryption. Sixty percent in Canada and 73 percent in the US believe “it’s only a matter of time” before cybercriminals are using the power of quantum to decrypt and disrupt today’s cybersecurity protocols. At the same time, however, 62 percent in Canada and 81 percent in the US admit that they need to do a better job of evaluating their current capabilities to ensure their data remains secure. 3
KPMG Australia research shows that protecting data and dealing with cyber risks is viewed by C-suite executives and board members from private sector enterprises as a top challenge in 2024 — and for the next 3 to 5 years.4
KPMG in Germany conducted research in collaboration with Germany’s Federal Office for Information Security (BSI), 95 percent of respondents believe quantum computing’s relevance and potential impact on today’s cryptographic security systems is “very high or high,” and 65 percent also say the average risk to their own data security is “very high or high.” Yet only 25 percent of firms say the threat posed is currently being addressed in their risk management strategy.5
The level of preparation that organizations do today is expected to be critical to limiting their exposure and vulnerability to emerging threats — making quantum risk planning a priority. Quantum computers can break encryption methods at an alarming speed, rendering ineffective encryption tools that are widely used today to protect everything from banking and retail transactions to business data, documents, email and more.
“Harvest-now, decrypt-later” attacks could enable adversaries to steal encrypted files and store them until more advanced quantum computers emerge.
KPMG firms are helping clients take action to understand and respond to the broad and unprecedented quantum-risk environment, as asymmetric encryption is used in multiple applications, from storage to communication. The risk landscape includes the following critical areas:
The quantum-risk landscape at a glance
There is little time to lose for organizations to gain a deeper understanding of the risks quantum may pose to their operations and security. For every organization that holds and processes data, they should consider the lifetime value of the data that they use, and the impact of that data being used or misrepresented by bad actors. For example:
"Quantum computing will upend the security infrastructure of the digital economy. Quantum technology in general promises to disrupt several areas of advanced technology and bring unprecedented capabilities that can be harnessed to improve the lives of people worldwide. At first glance it appears to be a curse to security, as cryptographic algorithms that proved to be secure for decades may be breached by quantum computers. This is in fact a blessing in disguise since this challenge gives us a much-needed impetus to build stronger and more-resilient foundations for the digital economy."
Dr. Michele Mosca
Institute for Quantum Computing
The University of Waterloo
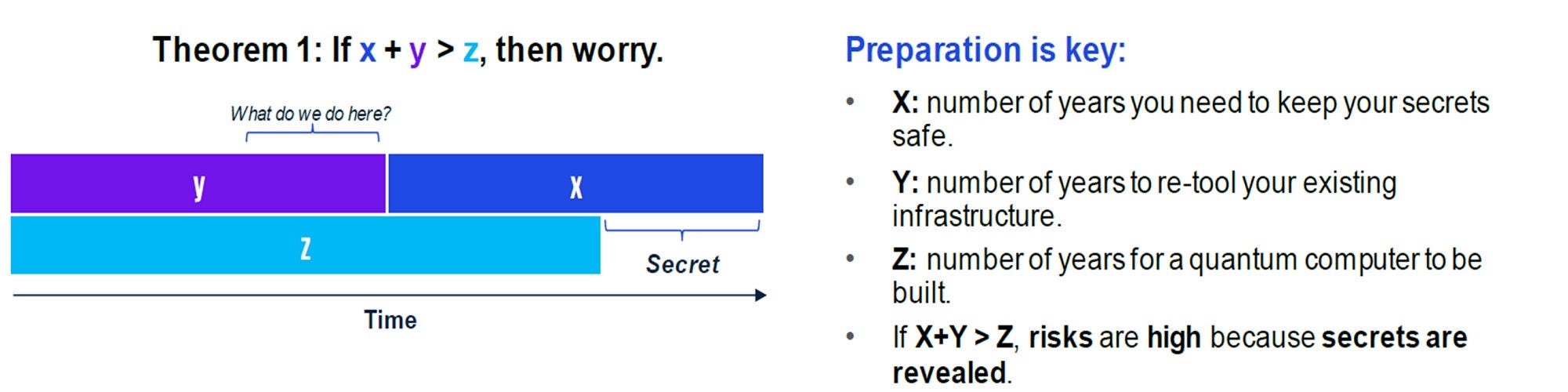
“Mosca’s Theorem”, illustrated below, suggests the timeframe required to protect data. Dr. Michele Mosca’s theorem stresses the need for organizations to begin applying diligence in the post-quantum space right away. It states that the amount of time that data must remain secure (X), plus the time it takes to upgrade cryptographic systems (Y), is greater than the time at which quantum computers have enough power to break cryptography (Z).
Once organizations are aware of their risk environment, they should be in a position to prioritize activity and mitigate or eliminate risks. However, this may not be a quick or simple process and may take years for each organization.
Managing technical debt, for example, can be a significant challenge for organizations relying on systems that will be incapable of running modern cryptographic profiles. There is now an opportunity to evaluate migration timelines and understand how long it will take to make infrastructure quantum resistant. To do this, organizations should understand the challenge and allocate budgets for both the mitigation and ongoing monitoring that the post-quantum world will require.
It’s critical that organizations not only prepare for the quantum threat in their long-term risk planning, but also strengthen data protection now to help minimize quantum’s potentially disruptive and costly impacts.
The rules of the game are changing to meet the new risk reality
As quantum emerges and organizations continue to explore and discover both its game-changing advantages and threats, new legislation and regulations are in the works. In 2022, a U.S. law was passed that requires government agencies to take action in using post-quantum cryptography — and encourages the private sector to follow suit7.
The National Institute of Standards and Technology (NIST) in December 2023 released two draft publications to guide organizations aiming to redefine their capabilities and combat potential quantum-based attacks. The documents — “Quantum Readiness: Cryptographic Discovery” and “Quantum Readiness: Testing Draft Standards for Interoperability and Performance” — outline concrete issues and potential solutions when migrating to a new post-quantum cryptographic standard.8
The growing list of initiatives also includes:
- The Quantum Computing Cybersecurity Preparedness Act 2022, advising US federal organizations to prepare now for a post-quantum cybersecurity (PQC) world;
- National Security Memorandum on “Promoting US Leadership in Quantum Computing While Mitigating Risk to Vulnerable Cryptographic Systems”;
- White House Memorandum on “Migration to Post-Quantum Cryptography”;
- Monetary Authority of Singapore MAS/TCRS/2024/01 : Advisory on Addressing the Cybersecurity Risks Associated with Quantum9;
- Quantum Security for the Financial Sector: Informing Global Regulatory Approaches, World Economic Forum in collaboration with the Financial Conduct Authority10.
This growing trend is likely to be investigated by other countries as we see a global movement towards identifying the risks and requirements of secure quantum technology.
Act now to help combat quantum’s risks
While quantum computing may seem like a futuristic science fiction concept, the technology is indeed poised to exert major consequences across today’s cybersecurity capabilities. We believe innovation is needed without delay.
The National Institute of Standards and Technology (NIST) has released a draft of the NIST Cybersecurity Framework 2.0 (CSF 2.0) — a major update to the Cyber Security Framework (CSF) it released in 2014 to help organizations reduce cybersecurity risk. To be finalized and published in early 2024, CSF 2.0 reflects changes in the cybersecurity landscape and will offer additional guidance on implementing the CSF.11
The NIST has also chosen four encryption tools that it says are designed “to withstand the assault of a future quantum computer, which could potentially crack the security used to protect privacy in the digital systems we rely on every day.” 12 The four encryption algorithms will become part of NIST’s post-quantum cryptographic standard and all are expected to be finalized and ready for use in 2024.13
Meanwhile, improvements and standards in Quantum Random Number Generators14 (QRNGs), for entropy enhancement and randomization, and Quantum Key Distribution,15 a secure communication method for exchanging encryption keys only known between shared parties, also aim to harness the power of quantum technology and protect data.
It’s important to note that today’s quantum solutions are creating a false sense of security — as we do not know if the quantum algorithms considered resistant will remain that way as quantum computers become larger and more mainstream. The danger is illustrated by the discovery of vulnerabilities in the NIST-selected encryption algorithm CRYSTALS-Kyber.16
Where to start as the power of quantum advances
Organizations can start to prepare by gaining a precise understanding of potential risks across their value chain. They should also identify methods to become more cryptographically agile in updating and deploying new cryptographic techniques as they become available. It’s also crucial to create end-of-life strategies for the data, products and systems that will become obsolete or unable to support new cybersecurity requirements in a quantum-computing world.
Here are key questions to ask going forward as quantum evolves:
Key actions to help mitigate quantum risks:
How KPMG can help
KPMG firms are helping organizations mitigate quantum risks. Our technology consulting specialists have extensive experience in cybersecurity and quantum technologies to support your quantum journey. Our quantum risk assessment can provide a deeper understanding of the specific threats posed by quantum technology.
With the help of KPMG firms, you can apply the outcomes of this assessment to build a customized cybersecurity strategy that fully encapsulates preparation for the quantum threat into your long-term risk planning — helping to prioritize your data and systems that are at risk. Steps to quantum-secure encryption include:
KPMG specialists are using our quantum readiness assessment methodology and innovative collaborations to help make a difference for clients. KPMG firms’ collaboration with IBM Quantum (Quantum Safe) and InfoSec Global allow us to begin understanding the cryptographic footprint/baseline and work towards remediation and potential digital solutions. KPMG specialists are here to help.
Related Content
Our People
1 https://home.kpmg/ca/en/home/market-insights/predictions/technology/quantum-computing-will-help-us-solve-our-most-difficult-problems.html
2 https://kpmg.com/ca/en/home/media/press-releases/2023/05/quantum-computing-is-coming-but-few-are-ready-for-it.html
3 Ibid.
4 https://assets.kpmg.com/content/dam/kpmg/au/pdf/2024/keeping-us-up-at-night-australian-business-leader-challenges-2024.pdf
5 https://www.bsi.bund.de/SharedDocs/Downloads/EN/BSI/Crypto/Marktumfrage_EN_Kryptografie_Quantencomputing.pdf?__blob=publicationFile&v=3
6 Mosca’s Theorem, Michele Mosca
7 Quantum Computing Cybersecurity Preparedness Act - This act addresses the migration of executive agencies' information technology systems to post-quantum cryptography.
8 https://www.nextgov.com/cybersecurity/2023/12/nist-releases-2-draft-guides-prepare-post-quantum-migration/392934/
9 https://www.mas.gov.sg/regulation/circulars/advisory-on-addressing-the-cybersecurity-risks-associated-with-quantum
10 https://www.weforum.org/publications/quantum-security-for-the-financial-sector-informing-global-regulatory-approaches/
11 https://csrc.nist.gov/projects/post-quantum-cryptography
12 https://www.nist.gov/news-events/news/2023/08/nist-standardize-encryption-algorithms-can-resist-attack-quantum-computers
13 Ibid.
14 https://phys.org/news/2023-05-quantum-random-generator-independently-source.html
15 https://quside.com/how-does-quantum-key-distribution-qkd-work/
16 https://eprint.iacr.org/2023/1084








