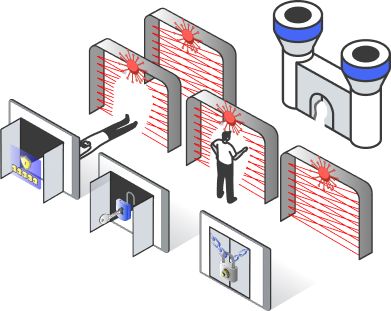
Cyber Threat Scenarios
How Cyber Risk Insights Works
Everything we do starts with a scenario. CRI comes with 12 pre-modelled Boolean logic-based scenarios out of the box. These include business email compromise, data breach and widespread ransomware. Get started quickly using the pre-modelled scenarios, or edit and create new ones using our intuitive scenario modeller.




HowCRIWorks.PDF 27/02/2023 254.8KB
Download the diagram as a PDF to enhance the visibility on small devices
Attacker contact rate
To calculate annualised likelihood, we estimate the credible number of attacker attempts in a given year for a specific scenario. There are two methods to do this - by perception and knowledge of the threat landscape, or with near-miss and incident data collected from your SOC.

Capability effectiveness
We designed a framework to help you consider capability effectiveness in a structured and repeatable manner.
For each capability, percentage effectiveness estimations are made across three components - process maturity, technical effectiveness and coverage.
Most likely and worst case loss
To model potential financial impact, we estimate the most likely and worst case loss should a particular scenario materialise.
Our impact calculator will help you decompose the loss and make estimates for different impact types using structured assumptions.
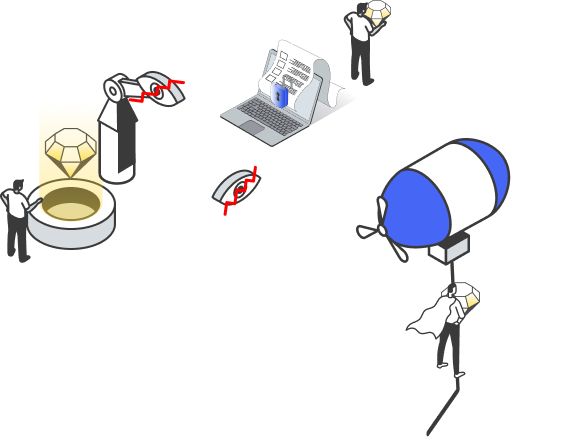
Bringing it all together
