The Cyber Resilience Act (CRA) is a European Union regulation aiming to strengthen the cybersecurity of digital products and software. The main purpose of CRA is to ensure that products with digital components are secure throughout their lifecycle, from design and development to post-market support.
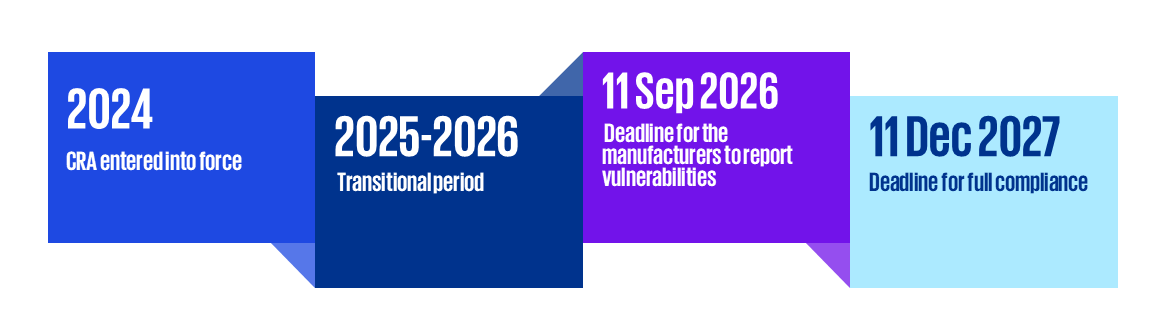
Timeline for the Cyber Resilience Act Implementation
Who is affected by the Cyber Resilience Act?
Cyber Resilience Act applies to all products with digital elements such as hardware, IoT, smart devices, and software including operating systems and applications, connected directly or indirectly to other devices or networks.
The regulation applies to manufacturers, importers, and distributors of digital products on the EU market, regardless of their origin.
Non-compliance can result in significant fines (up to €15 million or 2.5% of the global annual turnover).
Objectives of the regulation
- Harmonised standard for cyber security across the EU
- Increased overall cyber security of digital products on the internal market
- Improved consumer trust in digital products and services



